1
2
3
4
5
6
7
8
9
10
11
12
13
14
| tcpdump: data link type PKTAP
tcpdump: verbose output suppressed, use -v[v]... for full protocol decode
listening on pktap, link-type PKTAP (Apple DLT_PKTAP), snapshot length 524288 bytes
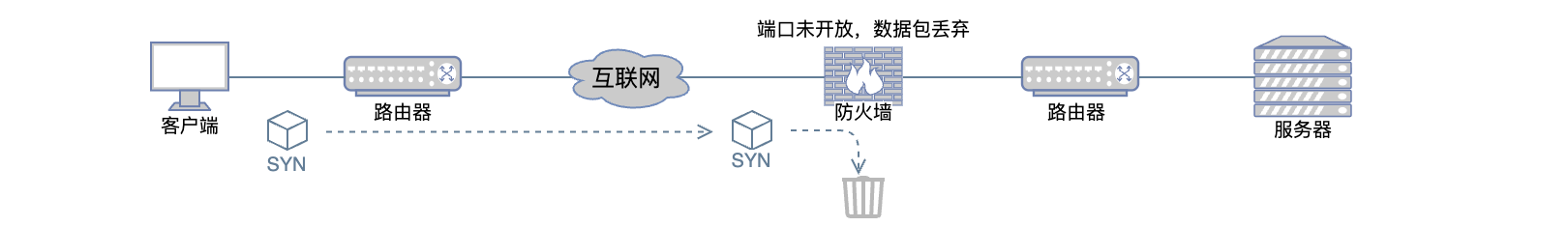
08:13:28.660606 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,nop,wscale 6,nop,nop,TS val 2553345619 ecr 0,sackOK,eol], length 0
08:13:29.660444 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,nop,wscale 6,nop,nop,TS val 2553346619 ecr 0,sackOK,eol], length 0
08:13:30.660923 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,nop,wscale 6,nop,nop,TS val 2553347620 ecr 0,sackOK,eol], length 0
08:13:31.660896 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,nop,wscale 6,nop,nop,TS val 2553348620 ecr 0,sackOK,eol], length 0
08:13:32.661747 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,nop,wscale 6,nop,nop,TS val 2553349621 ecr 0,sackOK,eol], length 0
08:13:33.662785 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,nop,wscale 6,nop,nop,TS val 2553350622 ecr 0,sackOK,eol], length 0
08:13:35.664588 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,nop,wscale 6,nop,nop,TS val 2553352623 ecr 0,sackOK,eol], length 0
08:13:39.665025 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,nop,wscale 6,nop,nop,TS val 2553356624 ecr 0,sackOK,eol], length 0
08:13:47.666382 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,nop,wscale 6,nop,nop,TS val 2553364625 ecr 0,sackOK,eol], length 0
08:14:03.666994 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,nop,wscale 6,nop,nop,TS val 2553380626 ecr 0,sackOK,eol], length 0
08:14:35.666851 IP 192.168.1.16.53461 > 100.108.149.128.yo-main: Flags [S], seq 2297239020, win 65535, options [mss 1460,sackOK,eol], length 0
|